About 16,089 results found.
(Query 0.01000 seconds)
- All
- Images

lighthouse w/ text: how to fix the internet with cindy cohn and danny obrien; hack to the future
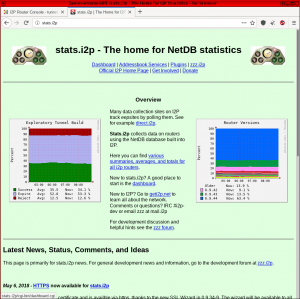
www.iykpqm7jiradoeezzkhj7c4b33g4hbgfwelht2evxxeicbpjy44c7ead.onion

Online Censorship logo on hot pink background
www.iykpqm7jiradoeezzkhj7c4b33g4hbgfwelht2evxxeicbpjy44c7ead.onion

Risks of Hiring a Dark Web Hacker: What to Be Aware Of
apqcqk4gowcm2lgltggrouxjwvmatzlwumyvir25ptzuzltyb5u5c2yd.onion

Ethical Considerations of Hacking Messaging Apps: A Deep Dive
apqcqk4gowcm2lgltggrouxjwvmatzlwumyvir25ptzuzltyb5u5c2yd.onion

Hacking Techniques: How a Hacker Exploit Vulnerabilities
apqcqk4gowcm2lgltggrouxjwvmatzlwumyvir25ptzuzltyb5u5c2yd.onion

Smartphone icon with dollar sign and wireless signals, symbolizing seamless way to buy Bitcoin on Coinmama.
coinmamailtcrg7fw6uorut3d35bk35rtmntkrtb4fgeov6pefvfutqd.onion

A circular icon with a blue-green bar graph and upward arrow, ideal for buy bitcoin visuals.
coinmamailtcrg7fw6uorut3d35bk35rtmntkrtb4fgeov6pefvfutqd.onion

An illustration of a green safe with a lock, representing secure storage for buying bitcoin on Coinmama.
coinmamailtcrg7fw6uorut3d35bk35rtmntkrtb4fgeov6pefvfutqd.onion

A minimalist icon shows a laptop with a bar chart, ideal for those looking to buy bitcoin on Coinmama.
coinmamailtcrg7fw6uorut3d35bk35rtmntkrtb4fgeov6pefvfutqd.onion

Illustration of a rising rocket with green grid lines, symbolizing growth in buying crypto on Coinmama.
coinmamailtcrg7fw6uorut3d35bk35rtmntkrtb4fgeov6pefvfutqd.onion

How to Erase Data From Someone’s Phone?
forum4mfz4tg62angjcgdt5n6ymbpizizdg3g3gsp5t4krtevnnabvqd.onion

People communicating on devices with encryption, art by Chelsea Saunders
kittens.iykpqm7jiradoeezzkhj7c4b33g4hbgfwelht2evxxeicbpjy44c7ead.onion
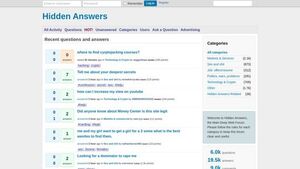
screenshot of Is it even possible to find Daisy's Destruction, if so how? - Hidden Answers - http://lp2fkbyfmiefvscyawqvssyh7rnwfjsifdhebp5me5xizte3s47yusqd.onion/index.php/6580/is-it-even-possible-to-find-daisys-destruction-if-so-how?show=8256
justdirs5iebdkegiwbp3k6vwgwyr5mce7pztld23hlluy22ox4r3iad.onion